Editor’s note: This article highlights 2018 Processing Breakthrough Products award winner Bedrock Automation OSA Remote controller, a solution for instrinsic cybersecurity.
Control systems change slowly. The basic design of a typical "modern" control system in service today is more than 20 years old. At that time, the internet was an infant. Amazon had just started selling books, Google had just surfaced and Facebook didn’t even exist. Today’s networked world didn’t exist yet either. Control system designers at the time assumed control networks would include only control devices. Bandwidth and processing power were limited and systems had to be isolated to ensure real-time performance. Security then meant just putting a fence around the plant perimeter and keeping the doors locked.
As a result, most of those same control system architectures that were dominant in the plant then are still dominant — but are intrinsically vulnerable to modern cyberattacks. A sufficiently knowledgeable attacker with network access can flip switches, adjust valves, change setpoints and even control strategies by sending messages directly to the control devices. Additionally, many control networks will have Windows workstations or other components whose security mechanisms and vulnerabilities are well known to hackers. This creates huge cyber vulnerabilities once the control network is no longer isolated.
But keeping a network isolated — creating a so-called air gap — is no longer realistic. Management wants data from the control system to be available across the enterprise. Vendors want remote access to devices they are maintaining. And plant engineers want remote access, so they can fix problems without having to drive to the plant at 2 a.m. These are just a few of the many ways increased connectivity improves plant performance, without even touching on more ambitious options afforded by future Internet of Things (IIoT) possibilities.
Borrowing from enterprise IT
The current standard practice is to borrow from the enterprise IT world. A firewall replaces the air gap between the control system and the enterprise network. More complex configurations will involve multiple firewalls, demilitarized zones (DMZs), virtual private networks (VPNs), network monitoring, intrusion detection systems and even remote cloud-based network monitoring. That originally air-gapped control network is now part of a very complex interconnected system that reaches all the way to the internet. If everything is well-configured and carefully maintained and monitored, the vulnerabilities associated with this huge attack surface can be managed to reduce risk. Setting up and maintaining this network infrastructure in the face of constantly changing cyber threats, however, requires serious sustained effort.
Russian hackers probe the power grid
A recent briefing by the U.S. Department of Homeland Security (DHS) and DHS Alert TA18-074A makes it clear that these defenses are penetrable. This report describes an extended Russian campaign against U.S. critical infrastructure.
The attackers began with extensive investigation of public websites and continued with phishing and watering hole attacks against both vendors and primary targets in the energy industry with particular emphasis on industrial control systems (ICS). The briefing slides showed a power plant control system HMI screen of a threat actor RDP session. It was reported to have been reconstructed from data left over from a Remote Desktop Protocol (RDP) session. The threat actor could have manipulated the controls on what appears to be a gas turbine generator running about a 15 Mw load.
This is not the only example. In 2015, attackers used RDP remote access to take down part of the Ukrainian power grid. In 2016 they did it again. In this case they used malware that communicated directly with the control devices. The Ukrainian authorities recently reported an attack by VPNfilter malware on a chemical plant. VPNfilter is malware installed on routers that includes a Modbus protocol module that communicates directly with control devices.
Trisis/Triton
Trisis (aka Triton) was an attack that reached the safety system of an unnamed chemical plant in the Middle East in 2017.
The attack targeted a Triconex safety system. Recently it was revealed that the attackers had been present in the plant networks for more than a year. The attackers seem to have used mostly ordinary hacking techniques to gain access to the control network. The attack on the Triconex controller was custom crafted. It is suspected that the process shutdown caused by the attacker’s manipulation of the controller was not the objective but an attacker mistake.
The identity and the motives of the attackers are unknown. What is known is that they were inside the plant networks long enough to find out almost anything they wanted to know about the plant and its control system. It is widely suspected the intent was to disable the safety system and then attack the process. The context is a large petrochemical complex. It is all too easy to imagine the pyrotechnics that might have been.
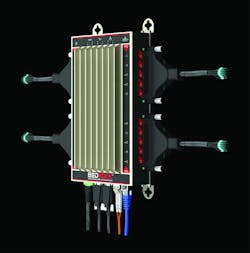
2018 Processing Breakthrough Products Award-winning OSA Remote controller embeds a public key infrastructure (PKI) at the chip level, which makes it responsible for its own security. Courtesy of Bedrock Automation
The growing threat landscape
These incidents illustrate both the limitations of present cyberdefense and the increasing interest in targeting ICS assets. Nation states are not the only actors. There is apparently an active market through which ordinary cybercriminals can sell indirect access to control systems. There is also malware designed to communicate directly with control devices that have no defenses. Once the perimeter defenses are penetrated the control network is a soft target. This problem is only going to get worse as the pressure to connect everything increases.
The IT world is also finding that the concept of a perimeter defense around a trusted interior is increasingly difficult to sustain. A few years ago, Google concluded that the solution was to assume the network could not be trusted. They launched a program they called BeyondCorp, which creates a new trust framework that does not rely on trusted networks. This has now evolved into a concept for the Zero Trust network. It computes access rights based on a trust score that includes the person, the device they are using, where they are located and what they have been doing recently. The employee using a personal laptop in a coffee shop has different privileges than he has from his office workstation inside a Google building. The Zero Trust solution evolved by Google and others is very complex, but the basic premise — that security cannot depend on trusting the network — is increasingly valid. Any device connected to a trusted network — even indirectly — becomes a potential attack vector.
The basic problem is simple: If we can’t trust the messenger — in this case, the network — how do we trust the message? The solution almost always comes down to answers to two questions: Who sent the message? And has it been tampered with? The digital technology to answer these questions is now ubiquitous, at least in the ecommerce, military and aerospace industries. It consists of a public key infrastructure (PKI) that can authenticate the sender and a variety of cryptographic algorithms that will ensure the message is tamperproof and private. But it is not yet built into the mainstream control systems that run most of global processing, primarily because these mainstream control architectures are deeply vested in the 20-year-old control technologies mentioned earlier.
How intrinsic cybersecurity works
2018 Processing Breakthrough Products Award winner Bedrock Automation is the exception. Bedrock embeds PKI into all of its devices starting at the chip level, making the device responsible for its own security. The system is no longer dependent on external, bolted-on network of firewalls, intrusion detection devices, etc., to parse out whether incoming signals can be trusted. This provides an entirely new level of depth to the defense. While elite hackers can bypass firewalls, breaking properly implemented strong cryptography is not a practical possibility. The attacker now faces a whole new set of barriers that exist on many signal paths, not just one. The controller essentially has an immune system.
The basic elements of PKI are straightforward. All trusted parties have unique certificates that identify them. The certificates also include data that defines each party’s system roles and privileges. Certificates are issued and managed by a certificate authority (CA). PKI mechanisms allow all members of the trust web to recognize other members and exclude imposters.
In the case of a controller module in an ICS, this security makes it possible to know that the actor is an engineer allowed to change the user programming, or if an operator has permission to change a setpoint. If the actor has the proper PKI credentials, the controller allows the action. If not, the controller blocks it.
The three battlefronts of intrinsic cybersecurity
Intrinsic security requires attention to security at three stages of development: the design of the system, the component supply chain and the manufacturing process.
Designing in security begins at the silicon level. Secure computing requires a tamperproof startup process. The first code the processor executes cannot be encrypted. Protecting this code with signatures or checksums doesn’t help because if it can be tampered with, the checks come too late. This initial code must be built into the microprocessor chip. Later phases can use code that is signed and encrypted, but this again requires special silicon features to protect the secret keys. Intrinsic security rests on a foundation laid at the silicon level.
At the silicon level, Bedrock has the unique visibility and control over their silicon supply chain that comes from designing and sourcing custom-manufactured chips. Their circuit boards are made and assembled in the United States. The origin and lot number of every part from microprocessors to resistors on every circuit board is tracked in Bedrock’s manufacturing database. Each board has a unique serial number. All boards are tested using special test fixtures and software.
Final assembly of modules is done at Bedrock’s secure facility. There, Bedrock loads each module with production software and a unique package of cryptographic certificates and keys bound to immutable features of its silicon. These key packages are generated by a special high-security computing system and loaded directly into the modules by a secure automated process. Each module now has its full cryptographic identity. It cannot be cloned or counterfeited. The module next goes through a first heat soak test. If all goes well, it is sealed into its tamper-resistant case and put through a final heat-soak test.
Deeper protection at lower cost
Firewalls, intrusion detection and connection technology each come with a price tag. They place a continuing maintenance and monitoring burden on operations, and still cannot defend against all evolving threats. Embedding cybersecurity deeply into the devices in a control system adds an additional robust layer of protection that does not depend on the security of the network layer. Operationally, this layer is almost cost-free. The added purchase cost of the devices is minimal, and the intrinsic security mechanisms are almost invisible to operations. Even if intruders get past the network defenses, they will likely be stopped in their tracks before they can do any damage.
Sam Galpin is a Bedrock Automation Fellow involved with advanced development and strategic planning and was principal software architect on the Bedrock Open Secure Automation (OSA) product line. Previously, he worked at the Foxboro Company (now part of Schneider Electric), where he wrote all software for the IA Series I/O modules and was lead software engineer on several other key control products. Prior to that he was CEO at Hyperform, a manufacturer of whitewater kayaks and canoes. Galpin holds a Bachelor of Science in earth science from MIT.